Resources to Guide You
When it comes to connecting technology to your business, we’re here to make your life easier. We’ve provided some resources to guide you in making great decisions.
10 Questions You Should Be Asking Your IT Provider Today
This article provides 10 questions that evaluate how your technology partner is optimizing your technology investment and taking care of you in the areas that matter most. Each question contains guidance on how to evaluate your technology partner’s responses and any potential risks you should watch for. At the bottom of this article, you will find an e-mail template you can copy and paste and send to your current provider for them to answer.
What You Should Know Before Migrating to the Cloud
The purpose of this brief guide is to provide business owners and decision makers a clear, easy-to-digest explanation of just what cloud computing is and the ways it improves how we do business. Tips are also provided for those who are seeking a cloud solutions specialist.
Regardless of who you choose for cloud-based solutions, it is never a decision you want to rush into without the proper analysis and strategy. By the end of this guide, you will have a better understanding of the cloud and the questions to ask when it comes to how cloud services can apply to your business.
InsITe’s Practical Security Defense Guide
Global attackers are targeting all organizations, large and small. And despite any intentions to store all data onsite, the reality is every organization’s employees are transmitting or storing organizational data externally on a regular basis; they simply may not know how or when.
In order to help recognize and prevent associated security breaches, our team of experienced security engineers have identified the top threats, and have provided tips to prevent breaches and vulnerabilities caused by these threats within this guide. Download this practical security defense guide to help you protect yourself today.
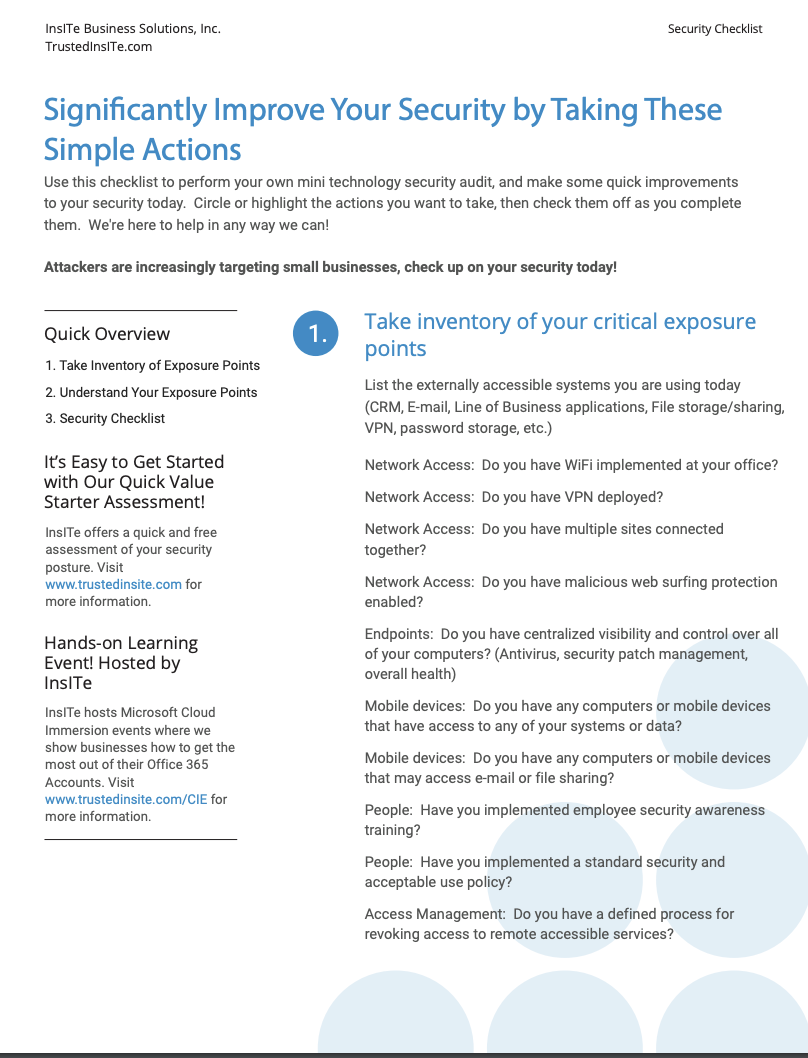
Security Check List
Use this checklist to perform your own mini technology security audit, and make some quick improvements to your security today. Circle or highlight the actions you want to take, then check them off as you complete them.
17 Things You Are Missing in Office 365
Why is Office 365 so under-utilized? Inexperienced and misguided technology providers. That’s right, the primary reason our new clients had not yet used some of these useful and business-impacting features of Office 365 is that their previous technology partner simply didn’t show them! Has your current technology provider shown you?
In our experience, a simple investment of one day of Office 365 training and feature demonstration time can unlock tens of thousands of dollars in value from a system you are already paying for.
The features called out in this article are designed to expose you to just some of the valuable pieces of Office 365, most of which you already own.
Connected Device Security Assessment Spreadsheet
Each device on your network can pose a potential threat to your entire network. And if your business is not secure, hackers can to get into every single device connected internally and control it. Before you know it, production is at a standstill.
In order to protect your connected devices, it’s important to assess which ones have been installed in operations and which systems they are connected to. One way to do that is by creating a detailed inventory list of your connected devices.
Download our free, easy-to-use Connected Device Security Assessment Spreadsheet that will help you list and assess all the devices you have, secure your operations, and identify possible threats that could come up.
Check out our blog to learn more about this topic!
Case Study: Audimute
Audimute determined it was time to update their server infrastructure and after some initial discovery, learned they had two options: purchase new servers, which is very costly, or invest in the cloud.
Audimute was looking for server hosting services and found InsITe through the Microsoft Partner Network. The company made it clear they needed help upgrading their server infrastructure and that they wanted to leverage the cloud, instead of relying on their onsite servers and network.
InsITe was able to eliminate the need for onsite servers, shifting Audimute to complete cloudnative infrastructure.
To see how InsITe was able to reduce TCO by 20% over 3 years and over 25% in management costs for Audimute, download the case study at the link below!
Case Study: Salem Tube
In order for Salem Tube to be successful, their technology needs to be highly available, secure, and focused around their unique needs as a leader in the industry.
InsITe provided the Azure Government subscription and configured the Azure Virtual Machines, Azure Virtual Networks, and connectivity, as well as Azure Backups to create a complete hosted environment for their SAP Hana application.
Click Below to see how we were able to accomplish…
- 100% ITAR Compliant SAP environment
- NIST 800-171 Capability
- Complete Remote Security
- Highly Redundant and Available Infrastructure
Case Study: Novo Building Products
Novo Building Products’ Azure cloud resources were not optimally configured and there was a potential for cost savings. Novo was also leveraging a SCE agreement for their cloud services, which locks them into a minimum spend for cloud services.
InsITe was able to perform a targeted assessment and measure Novo’s usage of each cloud resource, then compare the relative usage to the capacity of each resource.
To find out how InsITe reduced Novo’s cloud costs by 44% through targeted Azure optimizations, follow the link below!
Case Study: Gilda’s Club of Grand Rapids
Gilda’s Club Grand Rapids’ invoicing process required them to be on-site to both approve credit cards and physically file every payment order. When the pandemic hit, they realized they needed a better system to support their hybrid workforce and streamline their financial operations.
InsITe helped Gilda’s Club migrate this process to the cloud. This not only automated a lot of their time-consuming manual tasks and saved them hours in credit card approvals but helped secure any sensitive data.
Find out how Gilda’s Club reduced hours of invoicing into mere minutes using Microsoft Azure and Microsoft’s Power Platform.